Key Insights
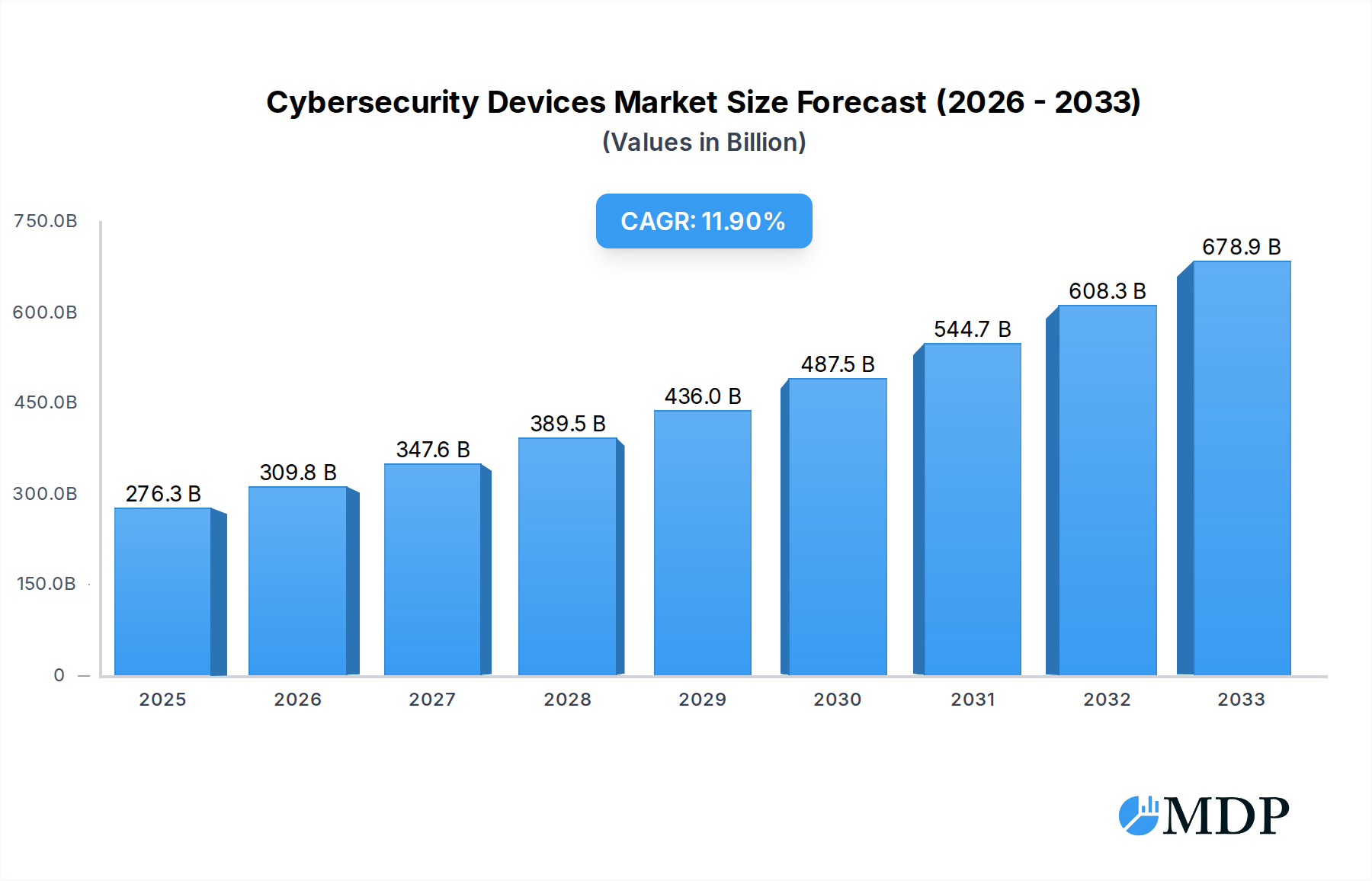
The global Cybersecurity Devices market is poised for significant expansion, projected to reach an estimated $276.25 billion by 2025. This robust growth is fueled by an accelerating compound annual growth rate (CAGR) of 12.13% over the forecast period of 2025-2033. The increasing sophistication and frequency of cyber threats, coupled with the growing volume of data generated and stored, necessitate advanced security solutions. Organizations across all sectors are prioritizing investments in cybersecurity devices to protect sensitive information, maintain operational continuity, and comply with stringent data privacy regulations. The rise of remote work, the proliferation of IoT devices, and the expanding cloud infrastructure further amplify the demand for comprehensive and adaptive cybersecurity measures. Key drivers include the escalating ransomware attacks, data breaches, and the growing awareness among businesses about the financial and reputational damage associated with cyber incidents.
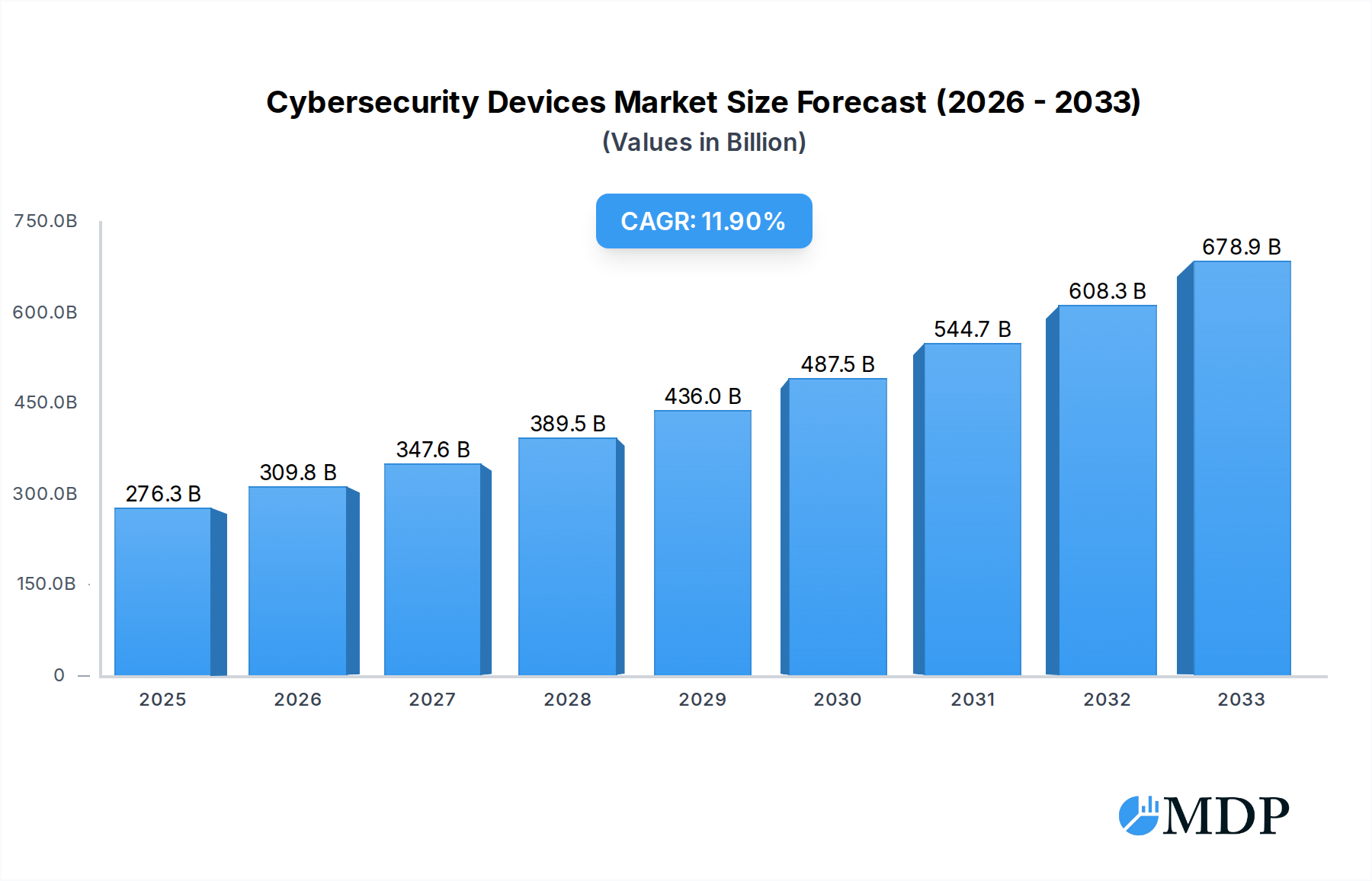
Cybersecurity Devices Market Size (In Billion)

The market is characterized by dynamic trends, including the integration of Artificial Intelligence (AI) and Machine Learning (ML) into cybersecurity devices for proactive threat detection and automated response. The increasing adoption of cloud-based security solutions, offering scalability and flexibility, is also a prominent trend. However, the market faces certain restraints, such as the high cost of advanced cybersecurity solutions, particularly for small and medium-sized enterprises, and the persistent shortage of skilled cybersecurity professionals. Despite these challenges, the market is expected to witness sustained demand driven by the continuous evolution of cyberattack vectors and the ongoing digital transformation across industries. Major players are actively engaged in research and development to introduce innovative products and services, including next-generation firewalls, intrusion detection/prevention systems, and advanced endpoint protection solutions, to meet the evolving security landscape.
Cybersecurity Devices Company Market Share

Unveiling the Future: A Comprehensive Report on the Global Cybersecurity Devices Market (2019-2033)
Report Description:
This in-depth analysis, the Cybersecurity Devices Market Report: Global Outlook 2019-2033, offers a definitive roadmap to the rapidly evolving landscape of cybersecurity hardware. With the global digital infrastructure facing unprecedented threats, this report provides actionable intelligence for industry stakeholders, including security vendors, enterprise IT decision-makers, government agencies, and investors. Spanning a comprehensive study period from 2019 to 2033, with a detailed focus on the base year 2025 and a robust forecast period of 2025-2033, this report leverages extensive historical data from 2019-2024 to illuminate current trends and project future trajectories. Discover the critical drivers of growth, the transformative impact of emerging technologies, and the competitive strategies employed by leading players in the multi-billion dollar cybersecurity devices market. This report delves into market segmentation by Application and Types, providing granular insights into specific product categories and their adoption across various industries. Furthermore, it dissects Industry Developments to offer a holistic understanding of the market's present and future. Expect unparalleled coverage of market dynamics, competitive concentration, innovation drivers, regulatory frameworks, and M&A activities, offering a true multi-billion dollar perspective.
Cybersecurity Devices Market Dynamics & Concentration
The cybersecurity devices market is characterized by a dynamic interplay of intense competition and strategic consolidation, with a projected market value in the hundreds of billions. While the industry is populated by a significant number of players, a concentrated core of leading companies holds substantial market share, driven by continuous innovation in threat detection and prevention. Key innovation drivers include the relentless evolution of cyber threats, the increasing sophistication of attack vectors, and the growing adoption of advanced technologies such as AI and machine learning in defense mechanisms. Regulatory frameworks, such as GDPR and CCPA, are increasingly mandating robust cybersecurity measures, further stimulating demand for advanced hardware solutions. Product substitutes, while present in the form of software-based security solutions, often complement hardware in a layered defense strategy. End-user trends indicate a strong preference for integrated security platforms and managed security services, pushing vendors towards comprehensive offerings. Mergers and acquisitions (M&A) are a significant aspect of market dynamics, with an estimated XX billion dollars in M&A deals recorded in the historical period, and an anticipated XX billion in the forecast period, aimed at expanding product portfolios, acquiring new technologies, and gaining market access. The market concentration is moderate to high, with the top 5 companies holding an estimated XX% market share in the historical period.
Cybersecurity Devices Industry Trends & Analysis
The cybersecurity devices industry is experiencing robust growth, projected to achieve a Compound Annual Growth Rate (CAGR) of approximately XX% from 2025 to 2033, contributing to a global market size exceeding hundreds of billions of dollars. This expansion is primarily fueled by the escalating frequency and severity of cyberattacks targeting both enterprises and individuals. Technological disruptions are at the forefront of this growth, with the integration of Artificial Intelligence (AI) and Machine Learning (ML) revolutionizing threat detection and response capabilities. These advancements enable real-time analysis of vast datasets, identifying anomalies and predicting potential threats with unprecedented accuracy, thereby enhancing the efficacy of devices like next-generation firewalls, intrusion detection systems, and endpoint protection hardware. Consumer preferences are increasingly leaning towards sophisticated, user-friendly security solutions that offer comprehensive protection across multiple devices and networks. The shift towards remote workforces and the proliferation of cloud-based services have further amplified the demand for secure access solutions and advanced network security hardware. Competitive dynamics are characterized by a fierce race for technological superiority, with companies heavily investing in research and development to introduce cutting-edge products and maintain a competitive edge. Market penetration is expanding rapidly across various sectors, including BFSI, healthcare, government, and IT, as organizations recognize the critical need to safeguard sensitive data and critical infrastructure. The increasing adoption of IoT devices also presents a significant growth avenue, necessitating specialized cybersecurity hardware to secure these connected ecosystems. The overall market penetration is estimated to reach XX% by 2033.
Leading Markets & Segments in Cybersecurity Devices
The global cybersecurity devices market is exhibiting strong leadership from the North America region, particularly the United States, which is projected to command a significant portion of the multi-billion dollar market share throughout the forecast period. This dominance is underpinned by a confluence of factors, including a mature digital economy, a high concentration of enterprises across critical sectors, and a proactive regulatory environment that mandates stringent cybersecurity compliance. Government initiatives and substantial investments in national cybersecurity infrastructure further bolster market leadership.
Within the Application segment, Network Security emerges as the dominant force. This is driven by the pervasive need for robust perimeter defenses, secure data transmission, and protection against network-borne threats. Key drivers for network security hardware include the increasing complexity of network architectures, the rise of distributed denial-of-service (DDoS) attacks, and the necessity for secure connectivity in an increasingly interconnected world. The adoption of technologies like Software-Defined Networking (SDN) and 5G further necessitates advanced network security devices like next-generation firewalls, intrusion prevention systems (IPS), and secure web gateways.
In terms of Types, Next-Generation Firewalls (NGFWs) are leading the market. These devices offer advanced threat prevention capabilities beyond traditional firewall functionalities, including deep packet inspection, application awareness, and integrated intrusion detection and prevention. Their widespread adoption is a direct response to the evolving threat landscape, where sophisticated malware and zero-day exploits are common. The economic policies favoring digital transformation and the increasing reliance on digital infrastructure by businesses across all sectors create a fertile ground for the growth of NGFWs. Furthermore, the continuous advancements in AI and ML integrated into these devices provide a significant competitive advantage, making them indispensable for organizations seeking to protect their digital assets.
Cybersecurity Devices Product Developments
Recent product developments in the cybersecurity devices market are characterized by a strong emphasis on integrated, AI-powered solutions. Companies are innovating in areas like endpoint detection and response (EDR) hardware that leverages machine learning to identify and neutralize threats in real-time, offering unparalleled protection against advanced persistent threats (APTs). Next-generation firewalls are evolving to incorporate more granular application control and threat intelligence sharing capabilities, enhancing network defense efficacy. The development of specialized hardware for securing IoT ecosystems, addressing the unique vulnerabilities of these devices, is also gaining traction. These innovations aim to provide proactive defense mechanisms, reduce the attack surface, and streamline security operations, offering significant competitive advantages to early adopters and driving market demand for advanced, intelligent security hardware.
Key Drivers of Cybersecurity Devices Growth
Several key drivers are propelling the growth of the cybersecurity devices market. The escalating sophistication and frequency of cyber threats, including ransomware, phishing, and advanced persistent threats (APTs), create an urgent need for robust hardware defenses. The increasing adoption of cloud computing and the Internet of Things (IoT) expands the attack surface, necessitating specialized security devices. Stringent regulatory compliance requirements, such as GDPR and HIPAA, mandate the implementation of advanced security measures, driving demand. Furthermore, the ongoing digital transformation across industries and the rise of remote work environments amplify the reliance on secure networks and endpoints, making advanced cybersecurity hardware indispensable.
Challenges in the Cybersecurity Devices Market
Despite robust growth, the cybersecurity devices market faces several challenges. The rapid pace of technological evolution means that security hardware can quickly become obsolete, leading to significant upgrade costs for organizations. Supply chain disruptions, particularly for specialized components, can impact production and availability, leading to delays and increased prices. The complexity of modern IT infrastructures can make seamless integration of new cybersecurity devices challenging, requiring significant expertise and resources. Furthermore, the intense competitive pressure can lead to price wars, impacting profit margins for vendors. The growing threat landscape also presents a constant arms race, requiring continuous innovation and substantial R&D investment, which can be a significant barrier for smaller players.
Emerging Opportunities in Cybersecurity Devices
Emerging opportunities in the cybersecurity devices market are primarily driven by technological breakthroughs and strategic market expansion. The widespread adoption of AI and machine learning is creating demand for intelligent security hardware capable of predictive threat analysis and automated response, opening avenues for advanced analytics platforms and AI-accelerated hardware. The burgeoning IoT market, with its vast array of connected devices, presents a significant opportunity for specialized security hardware solutions designed to protect vulnerable endpoints. Strategic partnerships between hardware vendors and cloud service providers are also emerging, offering integrated security solutions for cloud-based environments. Furthermore, the growing demand for managed security services (MSSPs) is creating opportunities for hardware vendors to offer integrated solutions that support these service providers.
Leading Players in the Cybersecurity Devices Sector
- Symantec Corporation
- McAfee LLC
- Trend Micro Incorporated
- Fortinet, Inc.
- Check Point Software Technologies Ltd.
- Sophos Ltd.
- F-Secure Corporation
- Kaspersky Lab
- Palo Alto Networks, Inc.
- Cisco Systems, Inc.
- Juniper Networks, Inc.
- FireEye, Inc.
- Proofpoint, Inc.
- Zscaler, Inc.
- CyberArk Software Ltd.
- Qualys, Inc.
- Avast PLC
- AVG Technologies
- ESET
- Avira Operations GmbH & Co. KG
- G DATA Software AG
- Barracuda Networks, Inc.
- Bitdefender
- RSA Security LLC
- Rapid7, Inc.
- Darktrace
- Carbon Black, Inc.
- Webroot Inc.
- SentinelOne, Inc.
- Cybereason Inc.
Key Milestones in Cybersecurity Devices Industry
- 2019 October: Launch of new AI-powered threat intelligence platform by Palo Alto Networks, enhancing network security capabilities.
- 2020 March: Fortinet acquires Marvis AI, further strengthening its capabilities in AI-driven network security automation.
- 2020 August: Cisco Systems unveils its SecureX platform, aiming to integrate its vast portfolio of security products.
- 2021 January: Check Point Software Technologies acquires Axonius, enhancing its asset management and cybersecurity posture.
- 2021 June: Trend Micro introduces new cloud security solutions, addressing the growing demand for cloud-native protection.
- 2022 February: Zscaler acquires Cloudneeti, expanding its cloud security capabilities.
- 2022 September: SentinelOne announces a significant funding round to accelerate its AI-driven endpoint security platform.
- 2023 April: Symantec Corporation (now Broadcom) continues to integrate its cybersecurity offerings, focusing on enterprise security solutions.
- 2023 November: McAfee LLC undergoes restructuring and strategic realignment, focusing on its core security products.
- 2024 January: FireEye (now Mandiant, acquired by Google) continues to focus on incident response and threat intelligence services.
- 2024 July: Proofpoint acquires a leading email security provider, enhancing its threat protection capabilities.
Strategic Outlook for Cybersecurity Devices Market
The strategic outlook for the cybersecurity devices market remains exceptionally strong, driven by the persistent and evolving nature of cyber threats. Future growth will be fueled by further integration of AI and machine learning into hardware for predictive analytics and autonomous threat response. The expansion of IoT and the increasing complexity of cloud environments will necessitate the development of specialized, scalable security solutions. Strategic partnerships and collaborations will be crucial for offering comprehensive, end-to-end security ecosystems. The market will witness a continued trend of consolidation, with leading players acquiring innovative technologies and expanding their global reach. Companies focusing on zero-trust architecture and proactive defense mechanisms will be well-positioned for sustained success in this multi-billion dollar sector.
Cybersecurity Devices Segmentation
- 1. Application
- 2. Types
Cybersecurity Devices Segmentation By Geography
-
1. Europe
- 1.1. United Kingdom
- 1.2. Germany
- 1.3. France
- 1.4. Italy
- 1.5. Spain
- 1.6. Netherlands
- 1.7. Belgium
- 1.8. Sweden
- 1.9. Norway
- 1.10. Poland
- 1.11. Denmark
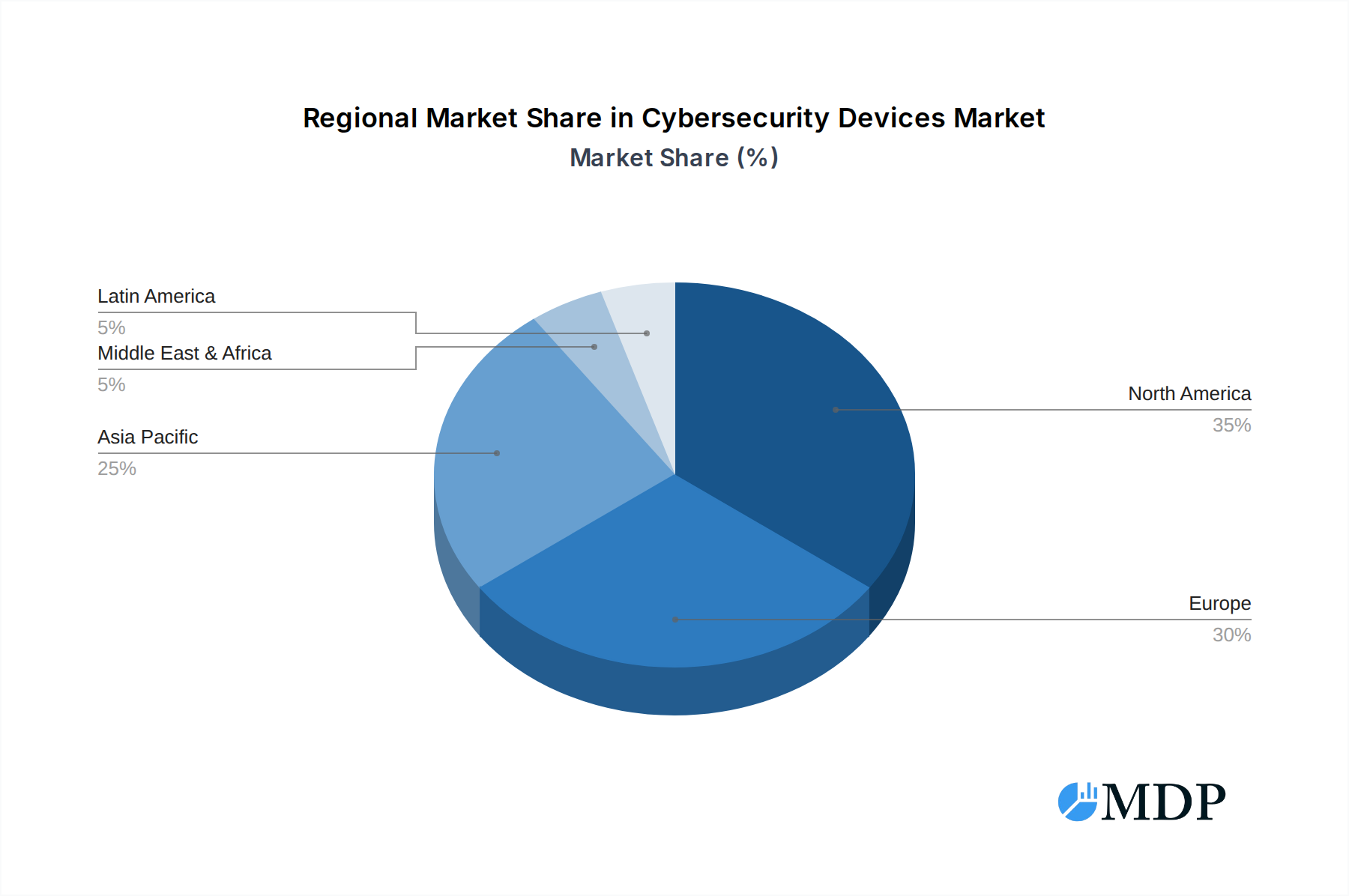
Cybersecurity Devices Regional Market Share

Geographic Coverage of Cybersecurity Devices
Cybersecurity Devices REPORT HIGHLIGHTS
| Aspects | Details |
|---|---|
| Study Period | 2020-2034 |
| Base Year | 2025 |
| Estimated Year | 2026 |
| Forecast Period | 2026-2034 |
| Historical Period | 2020-2025 |
| Growth Rate | CAGR of 12.13% from 2020-2034 |
| Segmentation |
|
Table of Contents
- 1. Introduction
- 1.1. Research Scope
- 1.2. Market Segmentation
- 1.3. Research Methodology
- 1.4. Definitions and Assumptions
- 2. Executive Summary
- 2.1. Introduction
- 3. Market Dynamics
- 3.1. Introduction
- 3.2. Market Drivers
- 3.3. Market Restrains
- 3.4. Market Trends
- 4. Market Factor Analysis
- 4.1. Porters Five Forces
- 4.2. Supply/Value Chain
- 4.3. PESTEL analysis
- 4.4. Market Entropy
- 4.5. Patent/Trademark Analysis
- 5. Cybersecurity Devices Analysis, Insights and Forecast, 2020-2032
- 5.1. Market Analysis, Insights and Forecast - by Application
- 5.2. Market Analysis, Insights and Forecast - by Types
- 5.3. Market Analysis, Insights and Forecast - by Region
- 5.3.1. Europe
- 5.1. Market Analysis, Insights and Forecast - by Application
- 6. Competitive Analysis
- 6.1. Market Share Analysis 2025
- 6.2. Company Profiles
- 6.2.1 Symantec Corporation
- 6.2.1.1. Overview
- 6.2.1.2. Products
- 6.2.1.3. SWOT Analysis
- 6.2.1.4. Recent Developments
- 6.2.1.5. Financials (Based on Availability)
- 6.2.2 McAfee LLC
- 6.2.2.1. Overview
- 6.2.2.2. Products
- 6.2.2.3. SWOT Analysis
- 6.2.2.4. Recent Developments
- 6.2.2.5. Financials (Based on Availability)
- 6.2.3 Trend Micro Incorporated
- 6.2.3.1. Overview
- 6.2.3.2. Products
- 6.2.3.3. SWOT Analysis
- 6.2.3.4. Recent Developments
- 6.2.3.5. Financials (Based on Availability)
- 6.2.4 Fortinet
- 6.2.4.1. Overview
- 6.2.4.2. Products
- 6.2.4.3. SWOT Analysis
- 6.2.4.4. Recent Developments
- 6.2.4.5. Financials (Based on Availability)
- 6.2.5 Inc.
- 6.2.5.1. Overview
- 6.2.5.2. Products
- 6.2.5.3. SWOT Analysis
- 6.2.5.4. Recent Developments
- 6.2.5.5. Financials (Based on Availability)
- 6.2.6 Check Point Software Technologies Ltd.
- 6.2.6.1. Overview
- 6.2.6.2. Products
- 6.2.6.3. SWOT Analysis
- 6.2.6.4. Recent Developments
- 6.2.6.5. Financials (Based on Availability)
- 6.2.7 Sophos Ltd.
- 6.2.7.1. Overview
- 6.2.7.2. Products
- 6.2.7.3. SWOT Analysis
- 6.2.7.4. Recent Developments
- 6.2.7.5. Financials (Based on Availability)
- 6.2.8 F-Secure Corporation
- 6.2.8.1. Overview
- 6.2.8.2. Products
- 6.2.8.3. SWOT Analysis
- 6.2.8.4. Recent Developments
- 6.2.8.5. Financials (Based on Availability)
- 6.2.9 Kaspersky Lab
- 6.2.9.1. Overview
- 6.2.9.2. Products
- 6.2.9.3. SWOT Analysis
- 6.2.9.4. Recent Developments
- 6.2.9.5. Financials (Based on Availability)
- 6.2.10 Palo Alto Networks
- 6.2.10.1. Overview
- 6.2.10.2. Products
- 6.2.10.3. SWOT Analysis
- 6.2.10.4. Recent Developments
- 6.2.10.5. Financials (Based on Availability)
- 6.2.11 Inc.
- 6.2.11.1. Overview
- 6.2.11.2. Products
- 6.2.11.3. SWOT Analysis
- 6.2.11.4. Recent Developments
- 6.2.11.5. Financials (Based on Availability)
- 6.2.12 Cisco Systems
- 6.2.12.1. Overview
- 6.2.12.2. Products
- 6.2.12.3. SWOT Analysis
- 6.2.12.4. Recent Developments
- 6.2.12.5. Financials (Based on Availability)
- 6.2.13 Inc.
- 6.2.13.1. Overview
- 6.2.13.2. Products
- 6.2.13.3. SWOT Analysis
- 6.2.13.4. Recent Developments
- 6.2.13.5. Financials (Based on Availability)
- 6.2.14 Juniper Networks
- 6.2.14.1. Overview
- 6.2.14.2. Products
- 6.2.14.3. SWOT Analysis
- 6.2.14.4. Recent Developments
- 6.2.14.5. Financials (Based on Availability)
- 6.2.15 Inc.
- 6.2.15.1. Overview
- 6.2.15.2. Products
- 6.2.15.3. SWOT Analysis
- 6.2.15.4. Recent Developments
- 6.2.15.5. Financials (Based on Availability)
- 6.2.16 FireEye
- 6.2.16.1. Overview
- 6.2.16.2. Products
- 6.2.16.3. SWOT Analysis
- 6.2.16.4. Recent Developments
- 6.2.16.5. Financials (Based on Availability)
- 6.2.17 Inc.
- 6.2.17.1. Overview
- 6.2.17.2. Products
- 6.2.17.3. SWOT Analysis
- 6.2.17.4. Recent Developments
- 6.2.17.5. Financials (Based on Availability)
- 6.2.18 Proofpoint
- 6.2.18.1. Overview
- 6.2.18.2. Products
- 6.2.18.3. SWOT Analysis
- 6.2.18.4. Recent Developments
- 6.2.18.5. Financials (Based on Availability)
- 6.2.19 Inc.
- 6.2.19.1. Overview
- 6.2.19.2. Products
- 6.2.19.3. SWOT Analysis
- 6.2.19.4. Recent Developments
- 6.2.19.5. Financials (Based on Availability)
- 6.2.20 Zscaler
- 6.2.20.1. Overview
- 6.2.20.2. Products
- 6.2.20.3. SWOT Analysis
- 6.2.20.4. Recent Developments
- 6.2.20.5. Financials (Based on Availability)
- 6.2.21 Inc.
- 6.2.21.1. Overview
- 6.2.21.2. Products
- 6.2.21.3. SWOT Analysis
- 6.2.21.4. Recent Developments
- 6.2.21.5. Financials (Based on Availability)
- 6.2.22 CyberArk Software Ltd.
- 6.2.22.1. Overview
- 6.2.22.2. Products
- 6.2.22.3. SWOT Analysis
- 6.2.22.4. Recent Developments
- 6.2.22.5. Financials (Based on Availability)
- 6.2.23 Qualys
- 6.2.23.1. Overview
- 6.2.23.2. Products
- 6.2.23.3. SWOT Analysis
- 6.2.23.4. Recent Developments
- 6.2.23.5. Financials (Based on Availability)
- 6.2.24 Inc.
- 6.2.24.1. Overview
- 6.2.24.2. Products
- 6.2.24.3. SWOT Analysis
- 6.2.24.4. Recent Developments
- 6.2.24.5. Financials (Based on Availability)
- 6.2.25 Avast PLC
- 6.2.25.1. Overview
- 6.2.25.2. Products
- 6.2.25.3. SWOT Analysis
- 6.2.25.4. Recent Developments
- 6.2.25.5. Financials (Based on Availability)
- 6.2.26 AVG Technologies
- 6.2.26.1. Overview
- 6.2.26.2. Products
- 6.2.26.3. SWOT Analysis
- 6.2.26.4. Recent Developments
- 6.2.26.5. Financials (Based on Availability)
- 6.2.27 ESET
- 6.2.27.1. Overview
- 6.2.27.2. Products
- 6.2.27.3. SWOT Analysis
- 6.2.27.4. Recent Developments
- 6.2.27.5. Financials (Based on Availability)
- 6.2.28 Avira Operations GmbH & Co. KG
- 6.2.28.1. Overview
- 6.2.28.2. Products
- 6.2.28.3. SWOT Analysis
- 6.2.28.4. Recent Developments
- 6.2.28.5. Financials (Based on Availability)
- 6.2.29 G DATA Software AG
- 6.2.29.1. Overview
- 6.2.29.2. Products
- 6.2.29.3. SWOT Analysis
- 6.2.29.4. Recent Developments
- 6.2.29.5. Financials (Based on Availability)
- 6.2.30 Barracuda Networks
- 6.2.30.1. Overview
- 6.2.30.2. Products
- 6.2.30.3. SWOT Analysis
- 6.2.30.4. Recent Developments
- 6.2.30.5. Financials (Based on Availability)
- 6.2.31 Inc.
- 6.2.31.1. Overview
- 6.2.31.2. Products
- 6.2.31.3. SWOT Analysis
- 6.2.31.4. Recent Developments
- 6.2.31.5. Financials (Based on Availability)
- 6.2.32 Bitdefender
- 6.2.32.1. Overview
- 6.2.32.2. Products
- 6.2.32.3. SWOT Analysis
- 6.2.32.4. Recent Developments
- 6.2.32.5. Financials (Based on Availability)
- 6.2.33 RSA Security LLC
- 6.2.33.1. Overview
- 6.2.33.2. Products
- 6.2.33.3. SWOT Analysis
- 6.2.33.4. Recent Developments
- 6.2.33.5. Financials (Based on Availability)
- 6.2.34 Rapid7
- 6.2.34.1. Overview
- 6.2.34.2. Products
- 6.2.34.3. SWOT Analysis
- 6.2.34.4. Recent Developments
- 6.2.34.5. Financials (Based on Availability)
- 6.2.35 Inc.
- 6.2.35.1. Overview
- 6.2.35.2. Products
- 6.2.35.3. SWOT Analysis
- 6.2.35.4. Recent Developments
- 6.2.35.5. Financials (Based on Availability)
- 6.2.36 Darktrace
- 6.2.36.1. Overview
- 6.2.36.2. Products
- 6.2.36.3. SWOT Analysis
- 6.2.36.4. Recent Developments
- 6.2.36.5. Financials (Based on Availability)
- 6.2.37 Carbon Black
- 6.2.37.1. Overview
- 6.2.37.2. Products
- 6.2.37.3. SWOT Analysis
- 6.2.37.4. Recent Developments
- 6.2.37.5. Financials (Based on Availability)
- 6.2.38 Inc.
- 6.2.38.1. Overview
- 6.2.38.2. Products
- 6.2.38.3. SWOT Analysis
- 6.2.38.4. Recent Developments
- 6.2.38.5. Financials (Based on Availability)
- 6.2.39 Webroot Inc.
- 6.2.39.1. Overview
- 6.2.39.2. Products
- 6.2.39.3. SWOT Analysis
- 6.2.39.4. Recent Developments
- 6.2.39.5. Financials (Based on Availability)
- 6.2.40 SentinelOne
- 6.2.40.1. Overview
- 6.2.40.2. Products
- 6.2.40.3. SWOT Analysis
- 6.2.40.4. Recent Developments
- 6.2.40.5. Financials (Based on Availability)
- 6.2.41 Inc.
- 6.2.41.1. Overview
- 6.2.41.2. Products
- 6.2.41.3. SWOT Analysis
- 6.2.41.4. Recent Developments
- 6.2.41.5. Financials (Based on Availability)
- 6.2.42 Cybereason Inc.
- 6.2.42.1. Overview
- 6.2.42.2. Products
- 6.2.42.3. SWOT Analysis
- 6.2.42.4. Recent Developments
- 6.2.42.5. Financials (Based on Availability)
- 6.2.1 Symantec Corporation
List of Figures
- Figure 1: Cybersecurity Devices Revenue Breakdown (undefined, %) by Product 2025 & 2033
- Figure 2: Cybersecurity Devices Share (%) by Company 2025
List of Tables
- Table 1: Cybersecurity Devices Revenue undefined Forecast, by Application 2020 & 2033
- Table 2: Cybersecurity Devices Revenue undefined Forecast, by Types 2020 & 2033
- Table 3: Cybersecurity Devices Revenue undefined Forecast, by Region 2020 & 2033
- Table 4: Cybersecurity Devices Revenue undefined Forecast, by Application 2020 & 2033
- Table 5: Cybersecurity Devices Revenue undefined Forecast, by Types 2020 & 2033
- Table 6: Cybersecurity Devices Revenue undefined Forecast, by Country 2020 & 2033
- Table 7: United Kingdom Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 8: Germany Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 9: France Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 10: Italy Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 11: Spain Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 12: Netherlands Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 13: Belgium Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 14: Sweden Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 15: Norway Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 16: Poland Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
- Table 17: Denmark Cybersecurity Devices Revenue (undefined) Forecast, by Application 2020 & 2033
Frequently Asked Questions
1. What is the projected Compound Annual Growth Rate (CAGR) of the Cybersecurity Devices?
The projected CAGR is approximately 12.13%.
2. Which companies are prominent players in the Cybersecurity Devices?
Key companies in the market include Symantec Corporation, McAfee LLC, Trend Micro Incorporated, Fortinet, Inc., Check Point Software Technologies Ltd., Sophos Ltd., F-Secure Corporation, Kaspersky Lab, Palo Alto Networks, Inc., Cisco Systems, Inc., Juniper Networks, Inc., FireEye, Inc., Proofpoint, Inc., Zscaler, Inc., CyberArk Software Ltd., Qualys, Inc., Avast PLC, AVG Technologies, ESET, Avira Operations GmbH & Co. KG, G DATA Software AG, Barracuda Networks, Inc., Bitdefender, RSA Security LLC, Rapid7, Inc., Darktrace, Carbon Black, Inc., Webroot Inc., SentinelOne, Inc., Cybereason Inc..
3. What are the main segments of the Cybersecurity Devices?
The market segments include Application, Types.
4. Can you provide details about the market size?
The market size is estimated to be USD XXX N/A as of 2022.
5. What are some drivers contributing to market growth?
N/A
6. What are the notable trends driving market growth?
N/A
7. Are there any restraints impacting market growth?
N/A
8. Can you provide examples of recent developments in the market?
N/A
9. What pricing options are available for accessing the report?
Pricing options include single-user, multi-user, and enterprise licenses priced at USD 3900.00, USD 5850.00, and USD 7800.00 respectively.
10. Is the market size provided in terms of value or volume?
The market size is provided in terms of value, measured in N/A.
11. Are there any specific market keywords associated with the report?
Yes, the market keyword associated with the report is "Cybersecurity Devices," which aids in identifying and referencing the specific market segment covered.
12. How do I determine which pricing option suits my needs best?
The pricing options vary based on user requirements and access needs. Individual users may opt for single-user licenses, while businesses requiring broader access may choose multi-user or enterprise licenses for cost-effective access to the report.
13. Are there any additional resources or data provided in the Cybersecurity Devices report?
While the report offers comprehensive insights, it's advisable to review the specific contents or supplementary materials provided to ascertain if additional resources or data are available.
14. How can I stay updated on further developments or reports in the Cybersecurity Devices?
To stay informed about further developments, trends, and reports in the Cybersecurity Devices, consider subscribing to industry newsletters, following relevant companies and organizations, or regularly checking reputable industry news sources and publications.
Methodology
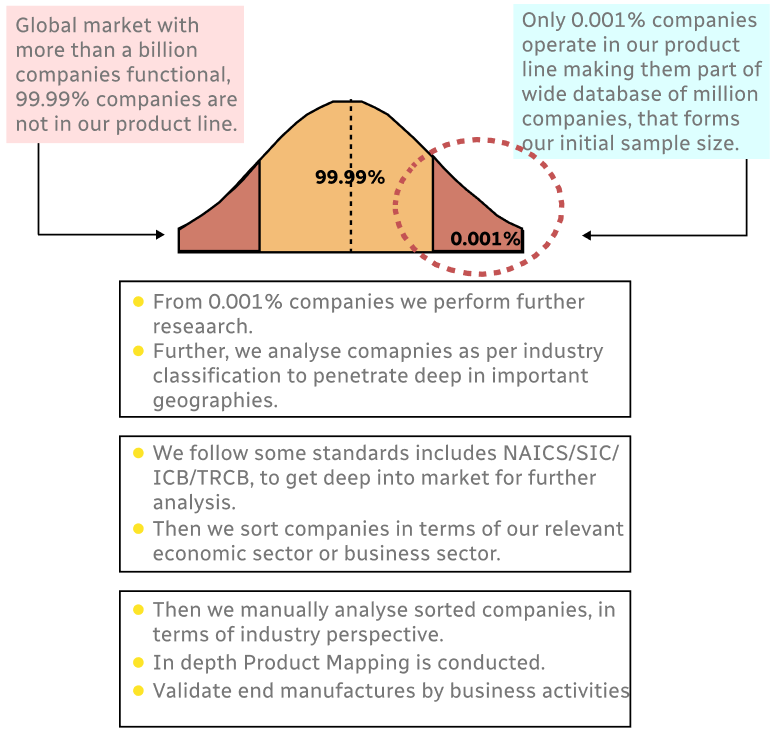
Step 1 - Identification of Relevant Samples Size from Population Database
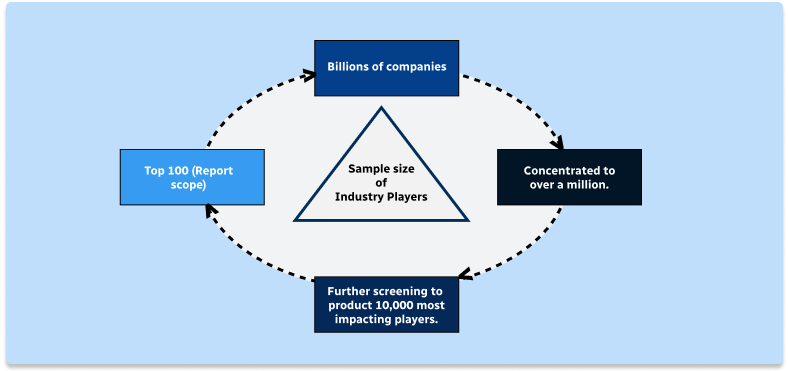
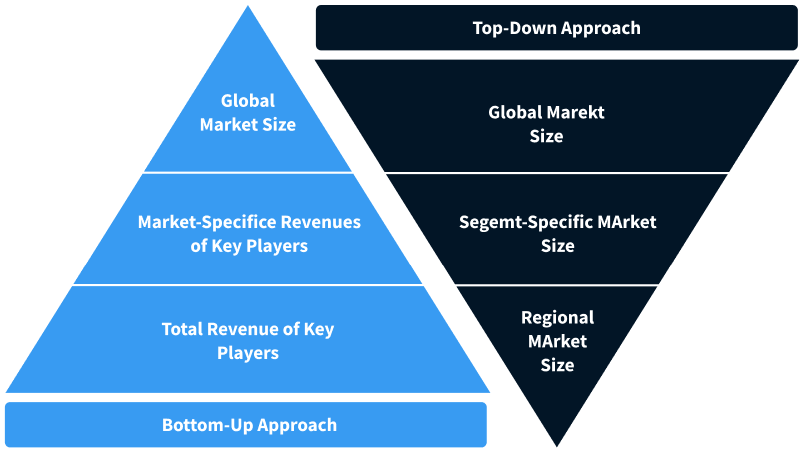
Step 2 - Approaches for Defining Global Market Size (Value, Volume* & Price*)
Note*: In applicable scenarios
Step 3 - Data Sources
Primary Research
- Web Analytics
- Survey Reports
- Research Institute
- Latest Research Reports
- Opinion Leaders
Secondary Research
- Annual Reports
- White Paper
- Latest Press Release
- Industry Association
- Paid Database
- Investor Presentations
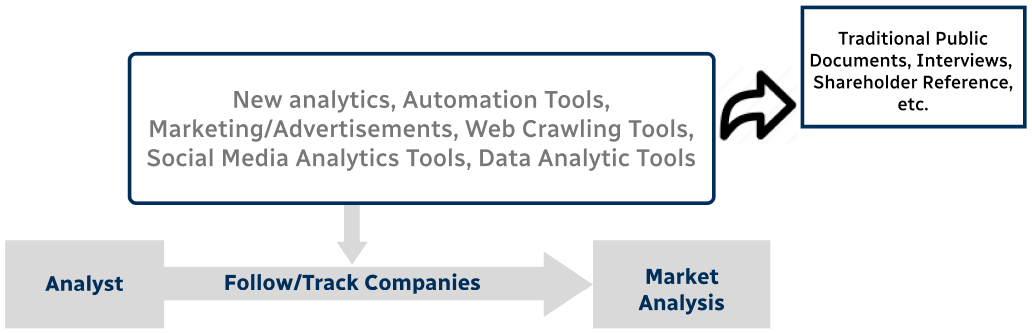
Step 4 - Data Triangulation
Involves using different sources of information in order to increase the validity of a study
These sources are likely to be stakeholders in a program - participants, other researchers, program staff, other community members, and so on.
Then we put all data in single framework & apply various statistical tools to find out the dynamic on the market.
During the analysis stage, feedback from the stakeholder groups would be compared to determine areas of agreement as well as areas of divergence


