Key Insights
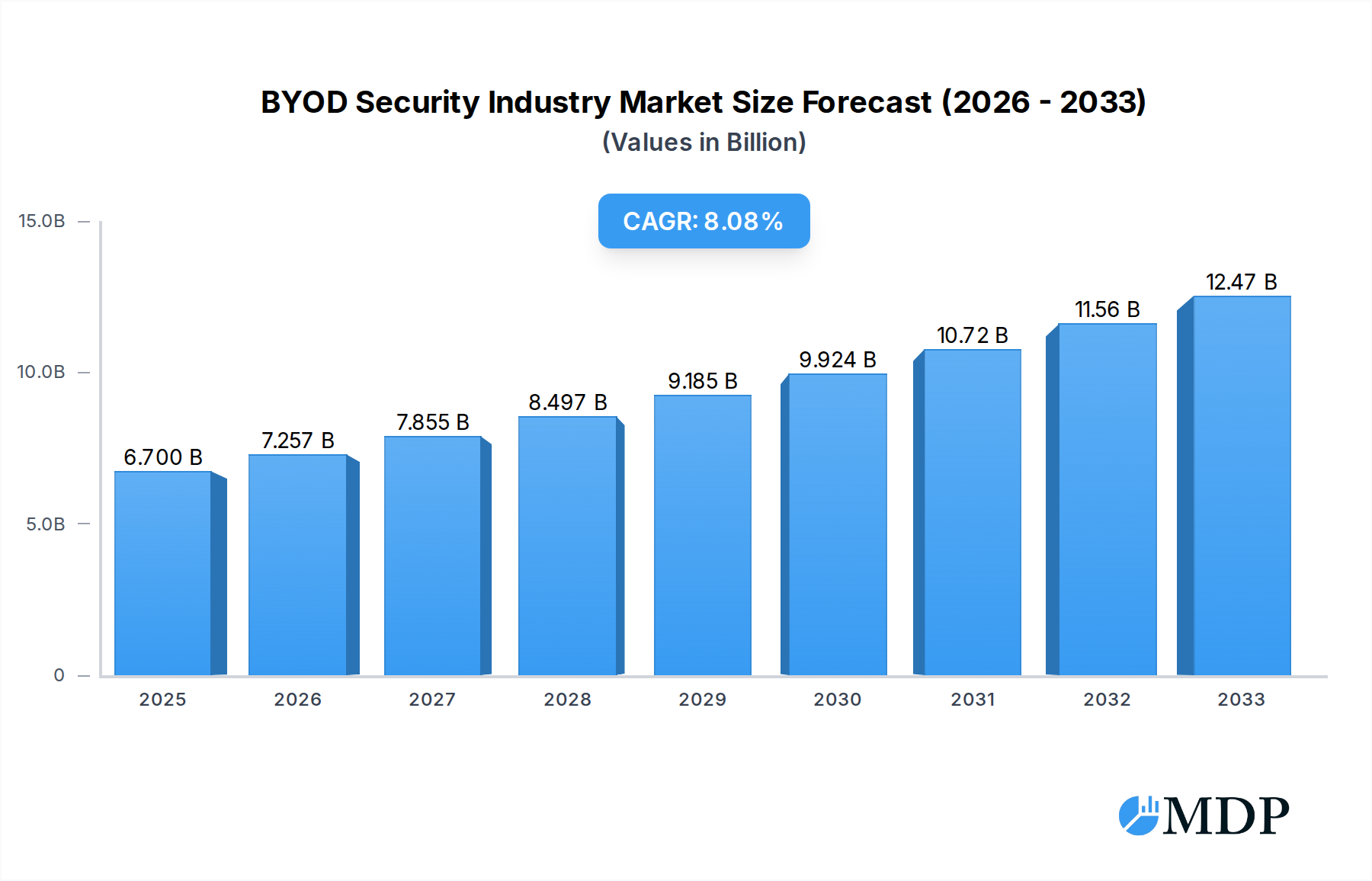
The Bring Your Own Device (BYOD) security market is poised for significant expansion, driven by the increasing adoption of flexible work policies and the pervasive use of personal devices in professional environments. The market is estimated to reach $6.7 billion in 2025, showcasing robust growth with a projected Compound Annual Growth Rate (CAGR) of 8.18% through 2033. This growth is fueled by escalating cybersecurity threats and the critical need for organizations to safeguard sensitive data accessed on a multitude of personal devices. Key drivers for this expansion include the rising complexity of the IT landscape, the demand for enhanced data protection, and the imperative for regulatory compliance. The market encompasses a comprehensive suite of solutions designed to secure the BYOD ecosystem, including Mobile Device Management (MDM), Mobile Application Management (MAM), Mobile Content Management (MCM), and Mobile Identity Management. These solutions are crucial for managing and protecting a diverse range of devices, from smartphones and tablets to laptops, ensuring that corporate data remains secure regardless of the access point. The software segment, encompassing Mobile Data Security, Mobile Device Security, and Network Security, forms another vital pillar of this market, providing the foundational layers of protection.
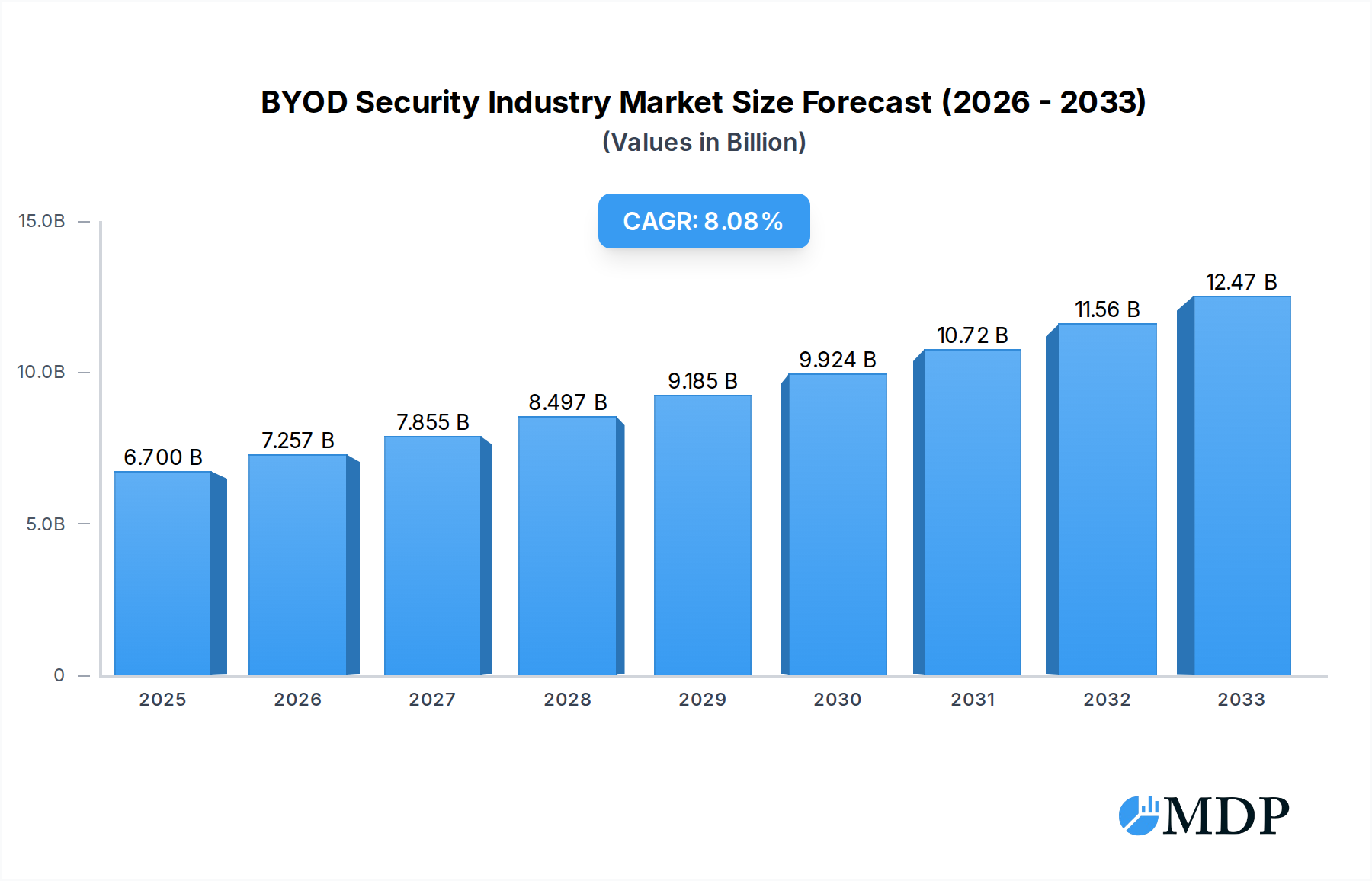
BYOD Security Industry Market Size (In Billion)

The BYOD security market is characterized by several dynamic trends. The increasing prevalence of sophisticated cyberattacks, such as ransomware and phishing attempts targeting mobile endpoints, necessitates advanced security measures. Organizations are increasingly investing in integrated security platforms that offer a holistic approach to managing and securing BYOD environments. Furthermore, the rise of remote and hybrid work models has amplified the importance of robust BYOD security strategies. Despite the optimistic outlook, certain restraints exist, including the potential for increased complexity in IT management, employee resistance to stringent security policies, and the ongoing challenge of keeping pace with evolving device technologies and their associated vulnerabilities. Major players in this competitive landscape include Forescout Technologies, IBM Corporation, Hewlett Packard Enterprise, Verizon Communications, Tata Consultancy Services Limited, Oracle Corporation, Cisco Systems, Aruba Networks, Blue Box, VMware Inc, and Citrix Systems Inc. The market's regional distribution indicates strong adoption in North America and Europe, with significant growth potential in the Asia Pacific region due to its rapidly expanding digital economy and increasing enterprise mobility.
BYOD Security Industry Company Market Share

This comprehensive report provides an in-depth analysis of the BYOD security industry, a critical sector for safeguarding enterprise data in the era of remote and hybrid work. Leveraging cutting-edge market intelligence, this study forecasts the market's trajectory from 2019 to 2033, with a base year of 2025 and a detailed forecast period of 2025-2033. We delve into the intricate dynamics, identifying key growth drivers, technological innovations, leading market players, and emerging opportunities. Essential for IT leaders, security professionals, investors, and solution providers, this report equips you with actionable insights to navigate the evolving BYOD security landscape.
BYOD Security Industry Market Dynamics & Concentration
The BYOD security industry is characterized by a dynamic interplay of innovation, regulatory compliance, and evolving end-user behaviors. Market concentration is moderate, with a few large players like IBM Corporation, Hewlett Packard Enterprise, and Cisco Systems holding significant market share, alongside a growing number of specialized vendors. Innovation drivers are primarily fueled by the escalating sophistication of cyber threats and the increasing adoption of mobile devices across all enterprise segments. Regulatory frameworks, such as GDPR and CCPA, are compelling organizations to implement robust BYOD security solutions, directly impacting market growth. Product substitutes, while present in the form of stringent corporate-owned device policies, are increasingly being overshadowed by the cost-effectiveness and flexibility of BYOD. End-user trends highlight a growing demand for seamless, user-friendly security that doesn't impede productivity. M&A activities are likely to remain robust as larger companies seek to acquire innovative technologies and expand their market reach, with an estimated xx M&A deal counts anticipated over the forecast period. Forescout Technologies, Verizon Communications, and Tata Consultancy Services Limited are among the prominent companies driving this competitive landscape.
BYOD Security Industry Industry Trends & Analysis
The BYOD security industry is experiencing a period of significant expansion, driven by a confluence of technological advancements and evolving workplace paradigms. The market is projected to witness a Compound Annual Growth Rate (CAGR) of approximately xx% during the forecast period (2025-2033), reflecting a strong and sustained demand for secure mobile device management. Market penetration of comprehensive BYOD security solutions is expected to surpass xx% by 2033, as organizations recognize the inherent risks associated with unmanaged personal devices accessing corporate networks. Key growth drivers include the proliferation of smartphones, tablets, and laptops in the workforce, necessitating robust security measures for each device category. Technological disruptions such as the advancement of AI and machine learning in threat detection, coupled with the increasing adoption of cloud-based security platforms, are revolutionizing how BYOD environments are secured. Consumer preferences are leaning towards solutions that offer a balance between security and user experience, prompting vendors to develop intuitive and less intrusive security protocols. Competitive dynamics are intensifying, with established players like Oracle Corporation and VMware Inc. competing alongside agile startups, all striving to capture market share through feature-rich and cost-effective offerings. The rise of sophisticated mobile threats, including advanced persistent threats (APTs) and ransomware targeting mobile endpoints, further amplifies the need for advanced BYOD security solutions. Aruba Networks and Citrix Systems Inc. are actively innovating to meet these evolving demands.
Leading Markets & Segments in BYOD Security Industry
The Smartphone segment is currently the dominant market within the BYOD security industry, driven by its ubiquitous presence across all professional demographics. This dominance is further bolstered by the inherent security challenges associated with smartphones, including the vast array of applications and the potential for lost or stolen devices. Mobile Device Management (MDM) solutions are the leading segment in terms of adoption, providing a foundational layer of security by enabling remote configuration, policy enforcement, and data encryption.
- Dominant Regions: North America currently leads the BYOD security market, attributed to its early adoption of mobile technologies, stringent data privacy regulations, and a high concentration of large enterprises. The Asia Pacific region is anticipated to exhibit the fastest growth due to rapid digital transformation and increasing mobile device penetration in emerging economies.
- Key Drivers for Dominance (Smartphones & MDM):
- Economic Policies: Favorable business environments encouraging technology adoption and investment in cybersecurity.
- Infrastructure: Widespread availability of high-speed mobile networks and cloud computing services.
- Regulatory Frameworks: Strict data protection laws mandating secure handling of sensitive information accessed via mobile devices.
- Technological Advancements: Continuous innovation in mobile hardware and software, demanding proportional security enhancements.
- Segment Dominance Analysis:
- Device: While Smartphones lead, Tablets are gaining traction for specific roles, and Laptops remain crucial for power users, each requiring tailored security approaches.
- Solution: MDM offers broad control, but Mobile Application Management (MAM), Mobile Content Management (MCM), and Mobile Identity Management are gaining prominence for granular security and enhanced user experience.
- Software: Mobile Data Security and Mobile Device Security are paramount, with Network Security playing an integral role in securing the overall BYOD ecosystem. Companies like Blue Box are contributing to specialized areas within this segment.
BYOD Security Industry Product Developments
The BYOD security industry is witnessing rapid product development focused on enhancing threat detection, streamlining user experience, and ensuring compliance. Innovations are centered around AI-powered anomaly detection, behavioral analytics for identifying suspicious user activities, and zero-trust architecture principles. Solutions are increasingly integrating advanced encryption techniques, secure containerization for sensitive data, and robust identity and access management (IAM) for multifactor authentication. Competitive advantages are derived from seamless integration with existing IT infrastructure, granular policy enforcement capabilities, and comprehensive reporting for audit and compliance purposes. The market is also seeing a rise in cloud-native BYOD security platforms, offering scalability and easier deployment.
Key Drivers of BYOD Security Industry Growth
The BYOD security industry's growth is propelled by several key factors. The escalating volume and sophistication of cyber threats targeting mobile endpoints necessitate robust defense mechanisms. The widespread adoption of remote and hybrid work models has made BYOD a standard practice, increasing the attack surface for organizations. Stringent data privacy regulations globally, such as GDPR and CCPA, mandate secure data handling and privacy, compelling enterprises to invest in BYOD security solutions. Furthermore, the cost-effectiveness and employee preference for using personal devices for work contribute to the sustained demand for secure BYOD environments. Technological advancements in mobile hardware and software also drive the need for updated security protocols.
Challenges in the BYOD Security Industry Market
Despite its robust growth, the BYOD security industry faces several challenges. Balancing security with user privacy and experience remains a significant hurdle; overly restrictive policies can lead to employee dissatisfaction and circumvention attempts. The rapid evolution of mobile operating systems and application landscapes requires constant updates and adaptation of security solutions, leading to increased development costs and potential vulnerabilities. Ensuring comprehensive compliance with diverse and evolving regulatory frameworks across different geographies adds complexity. Supply chain issues for hardware components and skilled cybersecurity talent shortages can also impact the development and deployment of effective BYOD security solutions, potentially leading to delays and increased operational costs.
Emerging Opportunities in BYOD Security Industry
Emerging opportunities in the BYOD security industry are ripe for innovation and strategic growth. The increasing integration of AI and machine learning for predictive threat intelligence and automated incident response presents a significant opportunity for vendors to offer more proactive and intelligent security solutions. The growing demand for Zero Trust security models within BYOD environments creates a need for granular access controls and continuous verification of user and device trust. Strategic partnerships between cybersecurity firms and mobile device manufacturers, as well as cloud service providers, can lead to integrated, end-to-end security solutions. Furthermore, expanding into underserved markets and offering specialized BYOD security solutions for niche industries like healthcare and finance represent significant growth avenues.
Leading Players in the BYOD Security Industry Sector
- Forescout Technologies
- IBM Corporation
- Hewlett Packard Enterprise
- Verizon Communications
- Tata Consultancy Services Limited
- Oracle Corporation
- Cisco Systems
- Aruba Networks
- Blue Box
- VMware Inc
- Citrix Systems Inc
Key Milestones in BYOD Security Industry Industry
- November 2022: Citrix released security upgrades to address a severe authentication bypass problem in its application delivery controller (ADC) and Gateway products used to take control of affected systems.
- November 2022: Allot Ltd. collaborated with Verizon to deliver network-based cybersecurity protection to portions of the company's wireless and fixed wireless Small and Medium Business (SMB) and Internet of Things (IoT) clients to protect them from a wide range of cyber-attacks.
Strategic Outlook for BYOD Security Industry Market
The strategic outlook for the BYOD security industry market is exceptionally positive, driven by the persistent need for secure mobile access in a globalized and digitally transformed business environment. The continuous evolution of cyber threats and the increasing adoption of flexible work policies will fuel ongoing demand for sophisticated BYOD security solutions. Organizations will increasingly prioritize integrated platforms that offer comprehensive device, application, and data security, alongside robust identity management. Investment in AI-driven threat detection and automated response mechanisms will become a key differentiator. Strategic partnerships and mergers are expected to consolidate the market, with a focus on acquiring innovative technologies and expanding global reach. The industry is poised for sustained growth as it adapts to new technological advancements and evolving security imperatives.
BYOD Security Industry Segmentation
-
1. Device
- 1.1. Smartphone
- 1.2. Tablet
- 1.3. Laptop
-
2. Solution
- 2.1. Mobile Device Management (MDM)
- 2.2. Mobile Application Management (MAM)
- 2.3. Mobile Content Management (MCM)
- 2.4. Mobile Identity Management
-
3. Software
- 3.1. Mobile Data Security
- 3.2. Mobile Device Security
- 3.3. Network Security
BYOD Security Industry Segmentation By Geography
- 1. North America
- 2. Europe
- 3. Asia Pacific
- 4. Latin America
- 5. Middle East and Africa
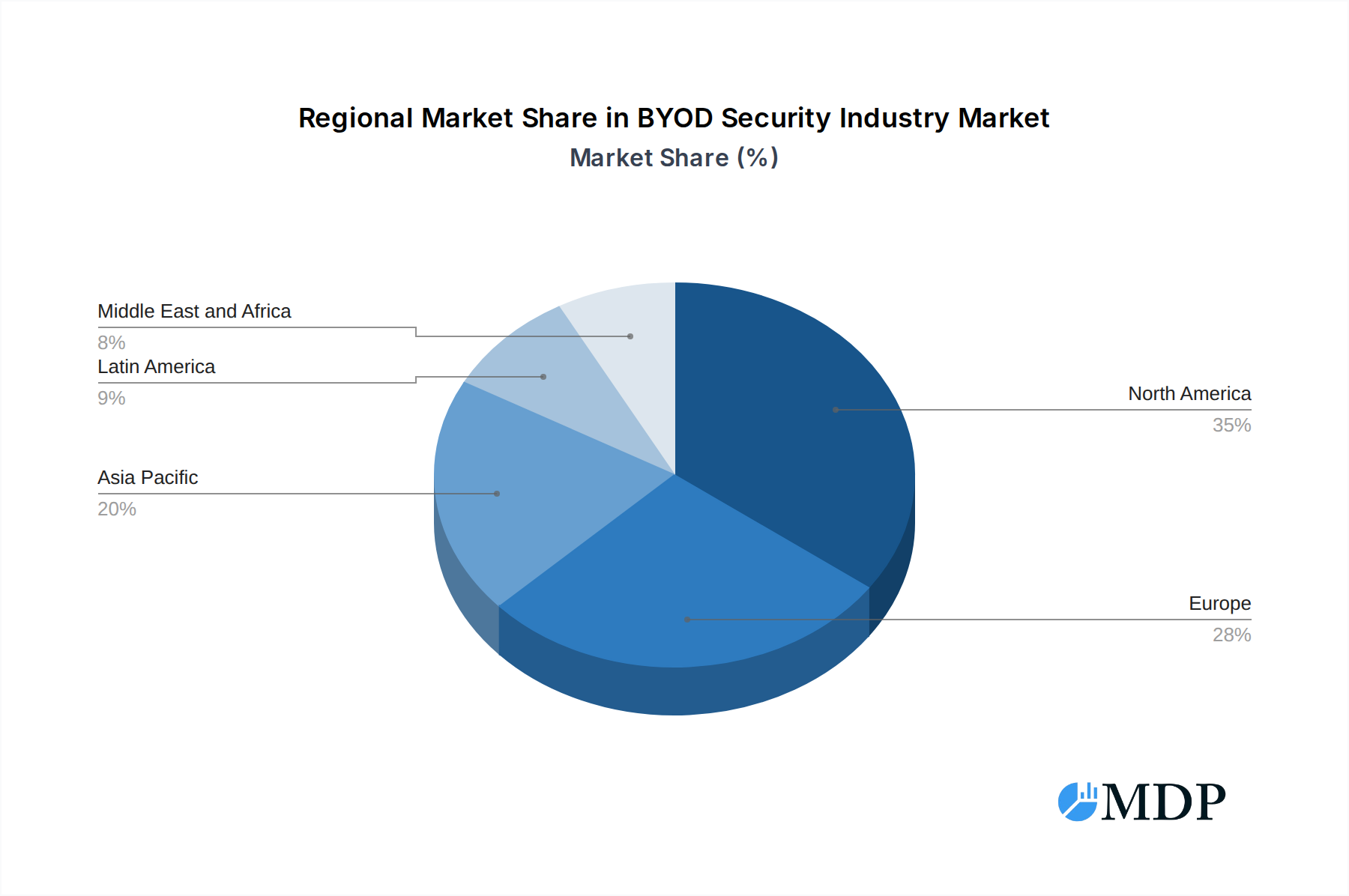
BYOD Security Industry Regional Market Share

Geographic Coverage of BYOD Security Industry
BYOD Security Industry REPORT HIGHLIGHTS
| Aspects | Details |
|---|---|
| Study Period | 2020-2034 |
| Base Year | 2025 |
| Estimated Year | 2026 |
| Forecast Period | 2026-2034 |
| Historical Period | 2020-2025 |
| Growth Rate | CAGR of 8.18% from 2020-2034 |
| Segmentation |
|
Table of Contents
- 1. Introduction
- 1.1. Research Scope
- 1.2. Market Segmentation
- 1.3. Research Objective
- 1.4. Definitions and Assumptions
- 2. Executive Summary
- 2.1. Market Snapshot
- 3. Market Dynamics
- 3.1. Market Drivers
- 3.2. Market Restrains
- 3.3. Market Trends
- 3.4. Market Opportunities
- 4. Market Factor Analysis
- 4.1. Porters Five Forces
- 4.1.1. Bargaining Power of Suppliers
- 4.1.2. Bargaining Power of Buyers
- 4.1.3. Threat of New Entrants
- 4.1.4. Threat of Substitutes
- 4.1.5. Competitive Rivalry
- 4.2. PESTEL analysis
- 4.3. BCG Analysis
- 4.3.1. Stars (High Growth, High Market Share)
- 4.3.2. Cash Cows (Low Growth, High Market Share)
- 4.3.3. Question Mark (High Growth, Low Market Share)
- 4.3.4. Dogs (Low Growth, Low Market Share)
- 4.4. Ansoff Matrix Analysis
- 4.5. Supply Chain Analysis
- 4.6. Regulatory Landscape
- 4.7. Current Market Potential and Opportunity Assessment (TAM–SAM–SOM Framework)
- 4.8. MDP Analyst Note
- 4.1. Porters Five Forces
- 5. Market Analysis, Insights and Forecast 2021-2033
- 5.1. Market Analysis, Insights and Forecast - by Device
- 5.1.1. Smartphone
- 5.1.2. Tablet
- 5.1.3. Laptop
- 5.2. Market Analysis, Insights and Forecast - by Solution
- 5.2.1. Mobile Device Management (MDM)
- 5.2.2. Mobile Application Management (MAM)
- 5.2.3. Mobile Content Management (MCM)
- 5.2.4. Mobile Identity Management
- 5.3. Market Analysis, Insights and Forecast - by Software
- 5.3.1. Mobile Data Security
- 5.3.2. Mobile Device Security
- 5.3.3. Network Security
- 5.4. Market Analysis, Insights and Forecast - by Region
- 5.4.1. North America
- 5.4.2. Europe
- 5.4.3. Asia Pacific
- 5.4.4. Latin America
- 5.4.5. Middle East and Africa
- 5.1. Market Analysis, Insights and Forecast - by Device
- 6. Global BYOD Security Industry Analysis, Insights and Forecast, 2021-2033
- 6.1. Market Analysis, Insights and Forecast - by Device
- 6.1.1. Smartphone
- 6.1.2. Tablet
- 6.1.3. Laptop
- 6.2. Market Analysis, Insights and Forecast - by Solution
- 6.2.1. Mobile Device Management (MDM)
- 6.2.2. Mobile Application Management (MAM)
- 6.2.3. Mobile Content Management (MCM)
- 6.2.4. Mobile Identity Management
- 6.3. Market Analysis, Insights and Forecast - by Software
- 6.3.1. Mobile Data Security
- 6.3.2. Mobile Device Security
- 6.3.3. Network Security
- 6.1. Market Analysis, Insights and Forecast - by Device
- 7. North America BYOD Security Industry Analysis, Insights and Forecast, 2020-2032
- 7.1. Market Analysis, Insights and Forecast - by Device
- 7.1.1. Smartphone
- 7.1.2. Tablet
- 7.1.3. Laptop
- 7.2. Market Analysis, Insights and Forecast - by Solution
- 7.2.1. Mobile Device Management (MDM)
- 7.2.2. Mobile Application Management (MAM)
- 7.2.3. Mobile Content Management (MCM)
- 7.2.4. Mobile Identity Management
- 7.3. Market Analysis, Insights and Forecast - by Software
- 7.3.1. Mobile Data Security
- 7.3.2. Mobile Device Security
- 7.3.3. Network Security
- 7.1. Market Analysis, Insights and Forecast - by Device
- 8. Europe BYOD Security Industry Analysis, Insights and Forecast, 2020-2032
- 8.1. Market Analysis, Insights and Forecast - by Device
- 8.1.1. Smartphone
- 8.1.2. Tablet
- 8.1.3. Laptop
- 8.2. Market Analysis, Insights and Forecast - by Solution
- 8.2.1. Mobile Device Management (MDM)
- 8.2.2. Mobile Application Management (MAM)
- 8.2.3. Mobile Content Management (MCM)
- 8.2.4. Mobile Identity Management
- 8.3. Market Analysis, Insights and Forecast - by Software
- 8.3.1. Mobile Data Security
- 8.3.2. Mobile Device Security
- 8.3.3. Network Security
- 8.1. Market Analysis, Insights and Forecast - by Device
- 9. Asia Pacific BYOD Security Industry Analysis, Insights and Forecast, 2020-2032
- 9.1. Market Analysis, Insights and Forecast - by Device
- 9.1.1. Smartphone
- 9.1.2. Tablet
- 9.1.3. Laptop
- 9.2. Market Analysis, Insights and Forecast - by Solution
- 9.2.1. Mobile Device Management (MDM)
- 9.2.2. Mobile Application Management (MAM)
- 9.2.3. Mobile Content Management (MCM)
- 9.2.4. Mobile Identity Management
- 9.3. Market Analysis, Insights and Forecast - by Software
- 9.3.1. Mobile Data Security
- 9.3.2. Mobile Device Security
- 9.3.3. Network Security
- 9.1. Market Analysis, Insights and Forecast - by Device
- 10. Latin America BYOD Security Industry Analysis, Insights and Forecast, 2020-2032
- 10.1. Market Analysis, Insights and Forecast - by Device
- 10.1.1. Smartphone
- 10.1.2. Tablet
- 10.1.3. Laptop
- 10.2. Market Analysis, Insights and Forecast - by Solution
- 10.2.1. Mobile Device Management (MDM)
- 10.2.2. Mobile Application Management (MAM)
- 10.2.3. Mobile Content Management (MCM)
- 10.2.4. Mobile Identity Management
- 10.3. Market Analysis, Insights and Forecast - by Software
- 10.3.1. Mobile Data Security
- 10.3.2. Mobile Device Security
- 10.3.3. Network Security
- 10.1. Market Analysis, Insights and Forecast - by Device
- 11. Middle East and Africa BYOD Security Industry Analysis, Insights and Forecast, 2020-2032
- 11.1. Market Analysis, Insights and Forecast - by Device
- 11.1.1. Smartphone
- 11.1.2. Tablet
- 11.1.3. Laptop
- 11.2. Market Analysis, Insights and Forecast - by Solution
- 11.2.1. Mobile Device Management (MDM)
- 11.2.2. Mobile Application Management (MAM)
- 11.2.3. Mobile Content Management (MCM)
- 11.2.4. Mobile Identity Management
- 11.3. Market Analysis, Insights and Forecast - by Software
- 11.3.1. Mobile Data Security
- 11.3.2. Mobile Device Security
- 11.3.3. Network Security
- 11.1. Market Analysis, Insights and Forecast - by Device
- 12. Competitive Analysis
- 12.1. Company Profiles
- 12.1.1 Forescout Technologies*List Not Exhaustive
- 12.1.1.1. Company Overview
- 12.1.1.2. Products
- 12.1.1.3. Company Financials
- 12.1.1.4. SWOT Analysis
- 12.1.2 IBM Corporation
- 12.1.2.1. Company Overview
- 12.1.2.2. Products
- 12.1.2.3. Company Financials
- 12.1.2.4. SWOT Analysis
- 12.1.3 Hewlett Packard Enterprise
- 12.1.3.1. Company Overview
- 12.1.3.2. Products
- 12.1.3.3. Company Financials
- 12.1.3.4. SWOT Analysis
- 12.1.4 Verizon Communicatiomns
- 12.1.4.1. Company Overview
- 12.1.4.2. Products
- 12.1.4.3. Company Financials
- 12.1.4.4. SWOT Analysis
- 12.1.5 Tata Consultancy Services Limited
- 12.1.5.1. Company Overview
- 12.1.5.2. Products
- 12.1.5.3. Company Financials
- 12.1.5.4. SWOT Analysis
- 12.1.6 Oracle Corporation
- 12.1.6.1. Company Overview
- 12.1.6.2. Products
- 12.1.6.3. Company Financials
- 12.1.6.4. SWOT Analysis
- 12.1.7 Cisco Systems
- 12.1.7.1. Company Overview
- 12.1.7.2. Products
- 12.1.7.3. Company Financials
- 12.1.7.4. SWOT Analysis
- 12.1.8 Aruba Networks
- 12.1.8.1. Company Overview
- 12.1.8.2. Products
- 12.1.8.3. Company Financials
- 12.1.8.4. SWOT Analysis
- 12.1.9 Blue Box
- 12.1.9.1. Company Overview
- 12.1.9.2. Products
- 12.1.9.3. Company Financials
- 12.1.9.4. SWOT Analysis
- 12.1.10 VMware Inc
- 12.1.10.1. Company Overview
- 12.1.10.2. Products
- 12.1.10.3. Company Financials
- 12.1.10.4. SWOT Analysis
- 12.1.11 Citrix Systems Inc
- 12.1.11.1. Company Overview
- 12.1.11.2. Products
- 12.1.11.3. Company Financials
- 12.1.11.4. SWOT Analysis
- 12.1.1 Forescout Technologies*List Not Exhaustive
- 12.2. Market Entropy
- 12.2.1 Company's Key Areas Served
- 12.2.2 Recent Developments
- 12.3. Company Market Share Analysis 2025
- 12.3.1 Top 5 Companies Market Share Analysis
- 12.3.2 Top 3 Companies Market Share Analysis
- 12.4. List of Potential Customers
- 13. Research Methodology
List of Figures
- Figure 1: Global BYOD Security Industry Revenue Breakdown (billion, %) by Region 2025 & 2033
- Figure 2: North America BYOD Security Industry Revenue (billion), by Device 2025 & 2033
- Figure 3: North America BYOD Security Industry Revenue Share (%), by Device 2025 & 2033
- Figure 4: North America BYOD Security Industry Revenue (billion), by Solution 2025 & 2033
- Figure 5: North America BYOD Security Industry Revenue Share (%), by Solution 2025 & 2033
- Figure 6: North America BYOD Security Industry Revenue (billion), by Software 2025 & 2033
- Figure 7: North America BYOD Security Industry Revenue Share (%), by Software 2025 & 2033
- Figure 8: North America BYOD Security Industry Revenue (billion), by Country 2025 & 2033
- Figure 9: North America BYOD Security Industry Revenue Share (%), by Country 2025 & 2033
- Figure 10: Europe BYOD Security Industry Revenue (billion), by Device 2025 & 2033
- Figure 11: Europe BYOD Security Industry Revenue Share (%), by Device 2025 & 2033
- Figure 12: Europe BYOD Security Industry Revenue (billion), by Solution 2025 & 2033
- Figure 13: Europe BYOD Security Industry Revenue Share (%), by Solution 2025 & 2033
- Figure 14: Europe BYOD Security Industry Revenue (billion), by Software 2025 & 2033
- Figure 15: Europe BYOD Security Industry Revenue Share (%), by Software 2025 & 2033
- Figure 16: Europe BYOD Security Industry Revenue (billion), by Country 2025 & 2033
- Figure 17: Europe BYOD Security Industry Revenue Share (%), by Country 2025 & 2033
- Figure 18: Asia Pacific BYOD Security Industry Revenue (billion), by Device 2025 & 2033
- Figure 19: Asia Pacific BYOD Security Industry Revenue Share (%), by Device 2025 & 2033
- Figure 20: Asia Pacific BYOD Security Industry Revenue (billion), by Solution 2025 & 2033
- Figure 21: Asia Pacific BYOD Security Industry Revenue Share (%), by Solution 2025 & 2033
- Figure 22: Asia Pacific BYOD Security Industry Revenue (billion), by Software 2025 & 2033
- Figure 23: Asia Pacific BYOD Security Industry Revenue Share (%), by Software 2025 & 2033
- Figure 24: Asia Pacific BYOD Security Industry Revenue (billion), by Country 2025 & 2033
- Figure 25: Asia Pacific BYOD Security Industry Revenue Share (%), by Country 2025 & 2033
- Figure 26: Latin America BYOD Security Industry Revenue (billion), by Device 2025 & 2033
- Figure 27: Latin America BYOD Security Industry Revenue Share (%), by Device 2025 & 2033
- Figure 28: Latin America BYOD Security Industry Revenue (billion), by Solution 2025 & 2033
- Figure 29: Latin America BYOD Security Industry Revenue Share (%), by Solution 2025 & 2033
- Figure 30: Latin America BYOD Security Industry Revenue (billion), by Software 2025 & 2033
- Figure 31: Latin America BYOD Security Industry Revenue Share (%), by Software 2025 & 2033
- Figure 32: Latin America BYOD Security Industry Revenue (billion), by Country 2025 & 2033
- Figure 33: Latin America BYOD Security Industry Revenue Share (%), by Country 2025 & 2033
- Figure 34: Middle East and Africa BYOD Security Industry Revenue (billion), by Device 2025 & 2033
- Figure 35: Middle East and Africa BYOD Security Industry Revenue Share (%), by Device 2025 & 2033
- Figure 36: Middle East and Africa BYOD Security Industry Revenue (billion), by Solution 2025 & 2033
- Figure 37: Middle East and Africa BYOD Security Industry Revenue Share (%), by Solution 2025 & 2033
- Figure 38: Middle East and Africa BYOD Security Industry Revenue (billion), by Software 2025 & 2033
- Figure 39: Middle East and Africa BYOD Security Industry Revenue Share (%), by Software 2025 & 2033
- Figure 40: Middle East and Africa BYOD Security Industry Revenue (billion), by Country 2025 & 2033
- Figure 41: Middle East and Africa BYOD Security Industry Revenue Share (%), by Country 2025 & 2033
List of Tables
- Table 1: Global BYOD Security Industry Revenue billion Forecast, by Device 2020 & 2033
- Table 2: Global BYOD Security Industry Revenue billion Forecast, by Solution 2020 & 2033
- Table 3: Global BYOD Security Industry Revenue billion Forecast, by Software 2020 & 2033
- Table 4: Global BYOD Security Industry Revenue billion Forecast, by Region 2020 & 2033
- Table 5: Global BYOD Security Industry Revenue billion Forecast, by Device 2020 & 2033
- Table 6: Global BYOD Security Industry Revenue billion Forecast, by Solution 2020 & 2033
- Table 7: Global BYOD Security Industry Revenue billion Forecast, by Software 2020 & 2033
- Table 8: Global BYOD Security Industry Revenue billion Forecast, by Country 2020 & 2033
- Table 9: Global BYOD Security Industry Revenue billion Forecast, by Device 2020 & 2033
- Table 10: Global BYOD Security Industry Revenue billion Forecast, by Solution 2020 & 2033
- Table 11: Global BYOD Security Industry Revenue billion Forecast, by Software 2020 & 2033
- Table 12: Global BYOD Security Industry Revenue billion Forecast, by Country 2020 & 2033
- Table 13: Global BYOD Security Industry Revenue billion Forecast, by Device 2020 & 2033
- Table 14: Global BYOD Security Industry Revenue billion Forecast, by Solution 2020 & 2033
- Table 15: Global BYOD Security Industry Revenue billion Forecast, by Software 2020 & 2033
- Table 16: Global BYOD Security Industry Revenue billion Forecast, by Country 2020 & 2033
- Table 17: Global BYOD Security Industry Revenue billion Forecast, by Device 2020 & 2033
- Table 18: Global BYOD Security Industry Revenue billion Forecast, by Solution 2020 & 2033
- Table 19: Global BYOD Security Industry Revenue billion Forecast, by Software 2020 & 2033
- Table 20: Global BYOD Security Industry Revenue billion Forecast, by Country 2020 & 2033
- Table 21: Global BYOD Security Industry Revenue billion Forecast, by Device 2020 & 2033
- Table 22: Global BYOD Security Industry Revenue billion Forecast, by Solution 2020 & 2033
- Table 23: Global BYOD Security Industry Revenue billion Forecast, by Software 2020 & 2033
- Table 24: Global BYOD Security Industry Revenue billion Forecast, by Country 2020 & 2033
Frequently Asked Questions
1. What is the projected Compound Annual Growth Rate (CAGR) of the BYOD Security Industry?
The projected CAGR is approximately 8.18%.
2. Which companies are prominent players in the BYOD Security Industry?
Key companies in the market include Forescout Technologies*List Not Exhaustive, IBM Corporation, Hewlett Packard Enterprise, Verizon Communicatiomns, Tata Consultancy Services Limited, Oracle Corporation, Cisco Systems, Aruba Networks, Blue Box, VMware Inc, Citrix Systems Inc.
3. What are the main segments of the BYOD Security Industry?
The market segments include Device, Solution, Software.
4. Can you provide details about the market size?
The market size is estimated to be USD 6.7 billion as of 2022.
5. What are some drivers contributing to market growth?
Increasing Smart Devices Penetration; Increasing Cyberattacks Drive the Demand for BYOD Security Solution.
6. What are the notable trends driving market growth?
Increasing Smart Devices Penetration.
7. Are there any restraints impacting market growth?
Security Concerns and Government Compliance.
8. Can you provide examples of recent developments in the market?
November 2022 - Citrix released security upgrades to address a severe authentication bypass problem in its application delivery controller (ADC) and Gateway products used to take control of affected systems.
9. What pricing options are available for accessing the report?
Pricing options include single-user, multi-user, and enterprise licenses priced at USD 4750, USD 5250, and USD 8750 respectively.
10. Is the market size provided in terms of value or volume?
The market size is provided in terms of value, measured in billion.
11. Are there any specific market keywords associated with the report?
Yes, the market keyword associated with the report is "BYOD Security Industry," which aids in identifying and referencing the specific market segment covered.
12. How do I determine which pricing option suits my needs best?
The pricing options vary based on user requirements and access needs. Individual users may opt for single-user licenses, while businesses requiring broader access may choose multi-user or enterprise licenses for cost-effective access to the report.
13. Are there any additional resources or data provided in the BYOD Security Industry report?
While the report offers comprehensive insights, it's advisable to review the specific contents or supplementary materials provided to ascertain if additional resources or data are available.
14. How can I stay updated on further developments or reports in the BYOD Security Industry?
To stay informed about further developments, trends, and reports in the BYOD Security Industry, consider subscribing to industry newsletters, following relevant companies and organizations, or regularly checking reputable industry news sources and publications.
Methodology
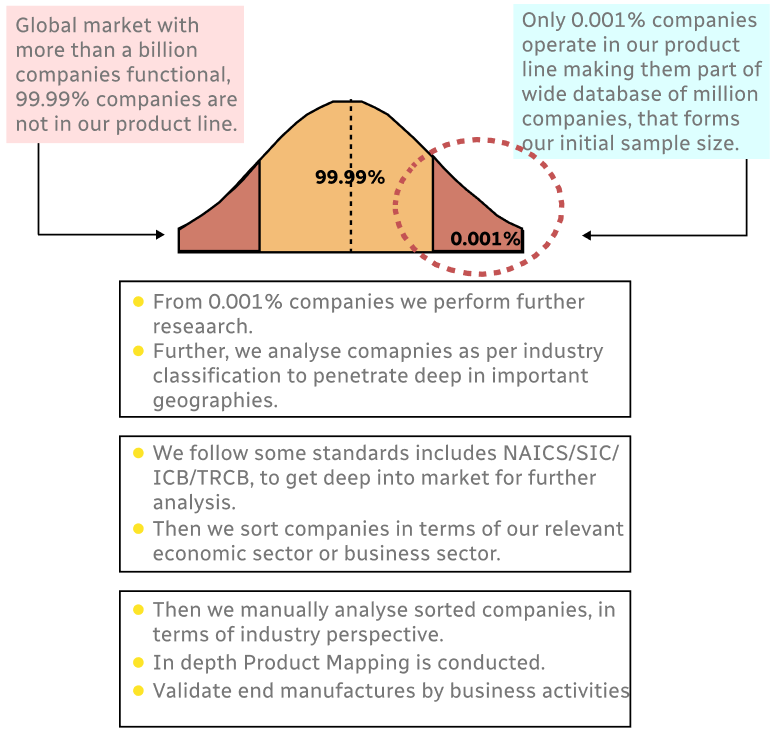
Step 1 - Identification of Relevant Samples Size from Population Database
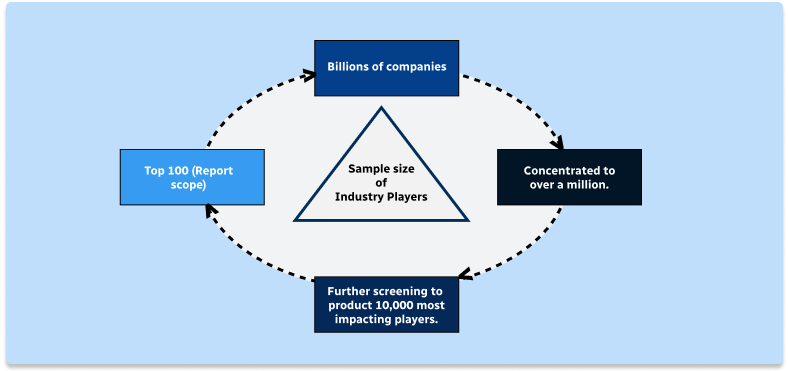
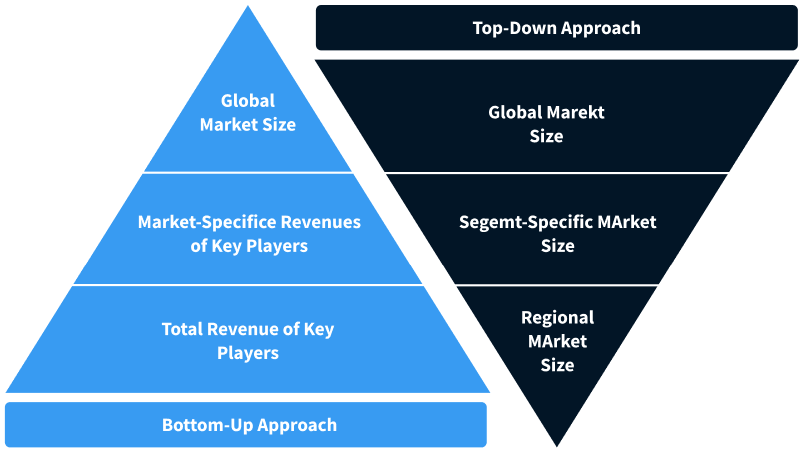
Step 2 - Approaches for Defining Global Market Size (Value, Volume* & Price*)
Note*: In applicable scenarios
Step 3 - Data Sources
Primary Research
- Web Analytics
- Survey Reports
- Research Institute
- Latest Research Reports
- Opinion Leaders
Secondary Research
- Annual Reports
- White Paper
- Latest Press Release
- Industry Association
- Paid Database
- Investor Presentations
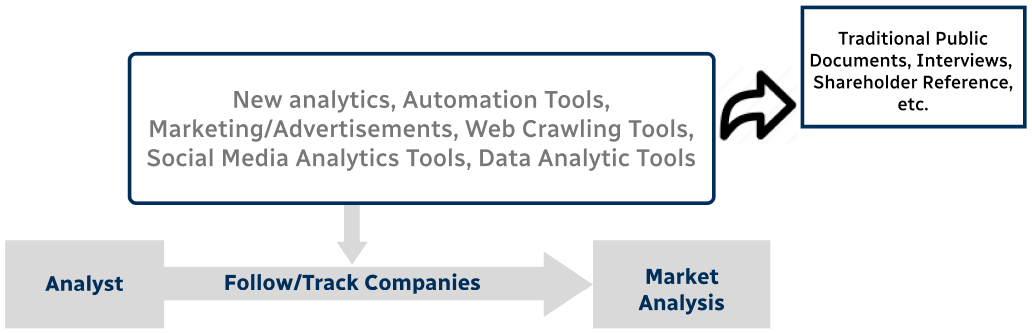
Step 4 - Data Triangulation
Involves using different sources of information in order to increase the validity of a study
These sources are likely to be stakeholders in a program - participants, other researchers, program staff, other community members, and so on.
Then we put all data in single framework & apply various statistical tools to find out the dynamic on the market.
During the analysis stage, feedback from the stakeholder groups would be compared to determine areas of agreement as well as areas of divergence


